Viewing the audit log
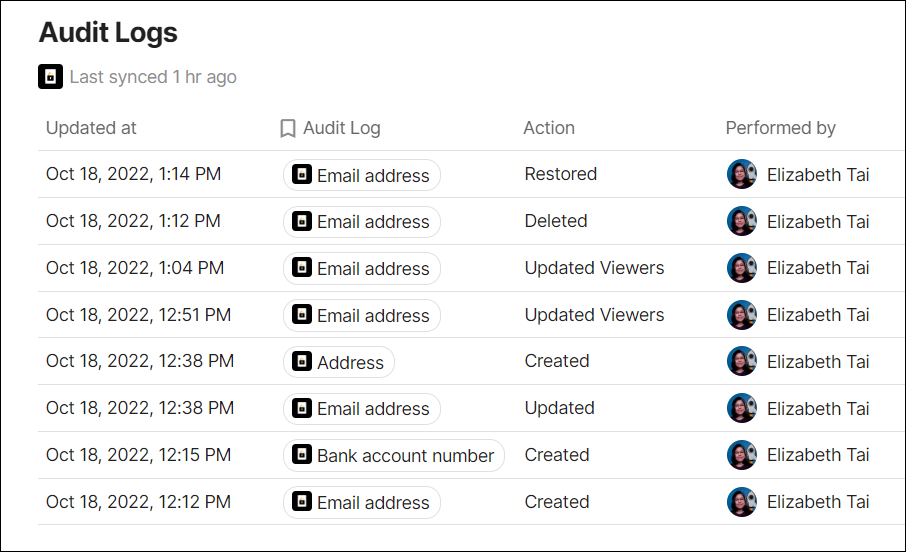
The audit log lists events around secrets: when they took place, who interacted, or who made changes to secrets.
You may use audit logs to run audit reports, review access to secrets, discover unintended access, detect suspicious activities or provide supporting evidence of your organization's security compliance.
Note
- Audit logs will be kept indefinitely.
- You can only display up to 10,000 rows of data.
Guide
- To view the Audit Log, navigate to the left sidebar of the doc and select Audit Log.
- You can then use Coda's table feature to perform the following functions:
- Filter data
- Sort data
- Edit columns
Audit log details
| Item | Description |
|---|---|
| Updated at | The date and time the event took place. (The timezone is automatically set to the user's settings.) |
| Secret Name | The name of the secret. |
| Action | The event that took place. It can be:
|
| Performed by | The viewer who performed the action. |
